Industrial Connectivity Has Changed; Security Models Haven’t
Operational technology (OT) environments power manufacturing plants, energy facilities, utilities, and other critical infrastructure systems around the world. These systems were built to prioritize reliability, safety, and deterministic control of physical processes and, in many cases, have operated for decades with minimal architectural change. What has changed dramatically is the connectivity surrounding those systems.
Industrial operations now depend on remote access for day-to-day work. Engineers troubleshoot equipment from remote locations, vendors maintain specialized industrial controllers, and operators require visibility into plant systems without being on site. As IT and OT environments converge, these access requirements have become embedded in normal operations and have introduced new risk into environments that were never designed for broad external connectivity.
Many OT systems rely on legacy hardware and proprietary protocols that cannot be patched or easily upgraded. Devices often remain in service long after vendor support ends, and taking them offline for maintenance may not be operationally feasible. At the same time, many industrial networks were designed as flat or lightly segmented environments where lateral communication between systems is common. When traditional remote access solutions are layered onto these architectures, the potential attack surface expands significantly.
The Limitations of Traditional Remote Access
For years, VPN technology has been the default approach for enabling remote connectivity. While VPNs provide encrypted access into a network, they were built around a model of network-level trust. Once a user authenticates, they typically gain visibility into large portions of the network. In IT environments, this exposure can sometimes be mitigated through segmentation and endpoint controls; in OT environments, those controls are often difficult to implement or maintain.
The result is a model where compromised credentials or misconfigured access policies can allow attackers to move laterally across industrial systems. This risk has become increasingly relevant as threat actors target industrial environments and critical infrastructure, frequently exploiting stolen credentials, over-permissioned accounts, and poorly controlled vendor access.
Compounding the problem, many organizations are hesitant to adopt cloud-brokered security architectures for OT networks. Routing industrial traffic through centralized cloud infrastructure can introduce latency or dependencies that may impact operational reliability and availability. What industrial environments require instead is a security model that tightly controls who can access specific systems, without introducing operational disruption.
Extending Zero Trust into OT Environments
Zero Trust Network Access (ZTNA) addresses this challenge by shifting the access model away from the network and toward identity. Rather than granting users broad access to an environment after authentication, ZTNA verifies users and devices and then allows connections only to explicitly authorized resources. Users never receive blanket network visibility, and unauthorized systems remain invisible.
This identity-centric approach significantly reduces the potential attack surface and prevents attackers from using compromised credentials to explore the environment. In OT environments, the impact can be especially pronounced. By controlling the access layer rather than attempting to redesign plant networks, organizations can introduce modern security controls without disrupting existing operational architectures.
However, industrial environments have requirements that differ from traditional enterprise networks. Performance, reliability, and architectural simplicity are critical considerations, and security controls must protect systems without interfering with the deterministic communication patterns that industrial operations depend on.
Why AppGate ZTNA Is Well Suited for OT Security
AppGate ZTNA extends identity centric Zero Trust principles into OT environments without disrupting sensitive operations or requiring complex network redesign. Built on a direct-routed architecture, it enables secure remote access to industrial systems while preserving the performance, availability, and operational integrity these environments demand. For organizations securing manufacturing plants, energy facilities, utilities, and other critical infrastructure, AppGate ZTNA provides a practical way to modernize access control around legacy systems, third-party access, and IT-to-OT convergence
- Identity-centric access control: AppGate authenticates and authorizes every user, including employees, contractors, and third-party vendors, before access to OT systems is permitted, eliminating implicit trust and ensuring users can access only the specific resources required for their role.
- Cloaked infrastructure: Protected industrial assets remain invisible to unauthorized users by leveraging a capability called single packet authorization, so services, ports, and internal IP addresses are never openly exposed and opportunities for reconnaissance are reduced.
- Granular, dynamic policies: Access can be restricted to specific systems, ports, and services based on user role, posture, time, and contextual factors, helping prevent the over-permissioned access that is common in VPN-based environments.
- Direct-routed architecture: AppGate establishes encrypted connections directly between authorized users and approved OT resources, avoiding backhaul through shared cloud brokers to support high-performance connectivity, preserve operational stability, and avoid unnecessary latency or third-party dependency risks.
- Lateral movement containment: By creating identity-defined micro-perimeters around OT resources, AppGate limits communication strictly to what policy allows, reducing the blast radius of compromised credentials or endpoints and helping contain threats before they spread across production systems.
- Support for complex industrial environments: AppGate integrates into existing OT architectures without requiring protocol conversion, plant network redesign, or disruption to established routing patterns, securing access to IP-reachable systems while preserving existing industrial controls, including segmentation boundaries and protocol gateways.
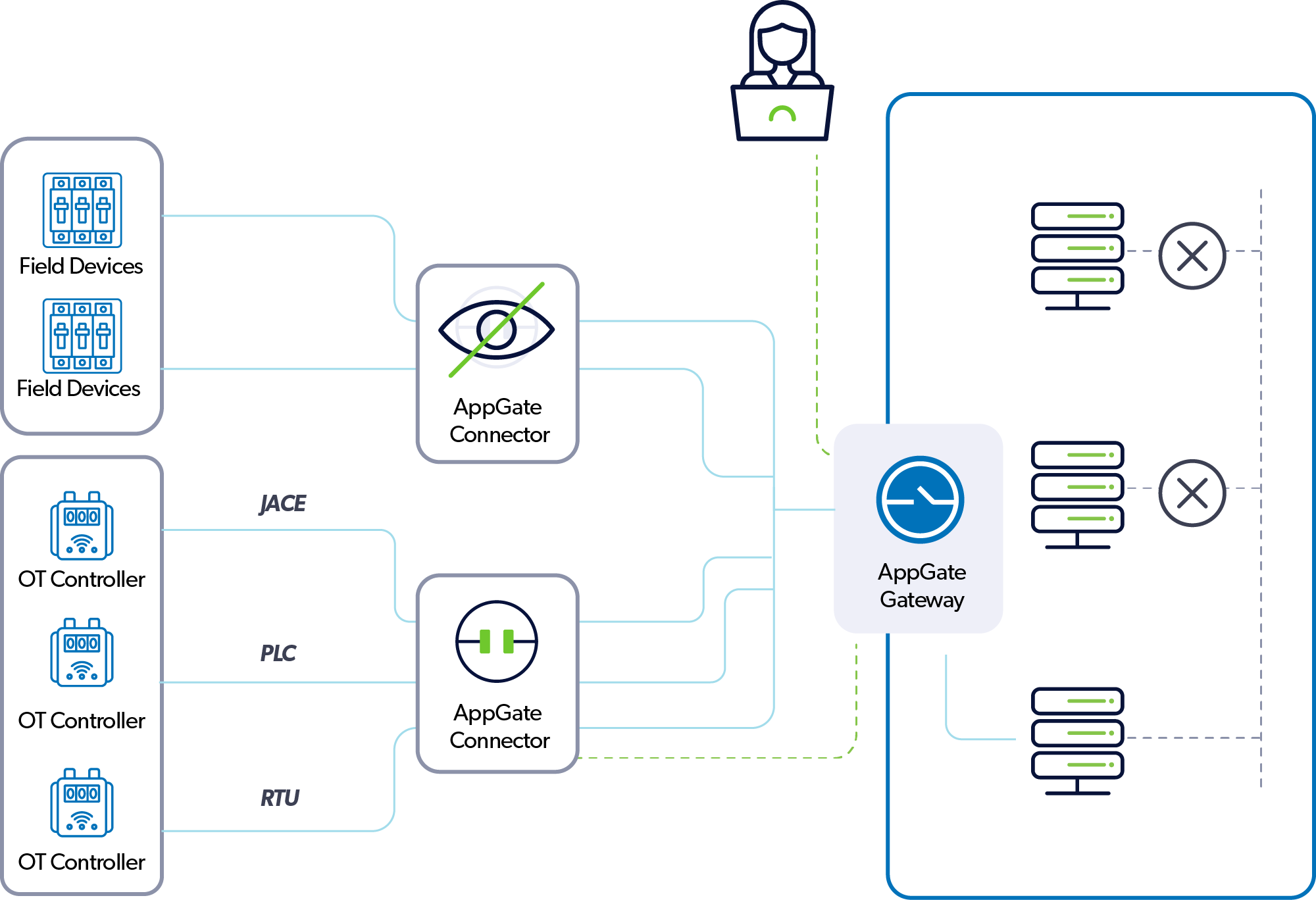
- Protection for legacy and unmanaged assets: For OT systems that cannot run the AppGate Client, the AppGate Connector extends secure, policy-driven access to legacy devices, remote sites, and unmanaged assets, acting as a secure bridge that enables authorized access without exposing protected systems to the broader network.
Securing Industrial Access Without Disrupting Operations
A key challenge in OT security is introducing stronger protections without forcing disruptive architectural changes. Industrial environments often depend on established routing designs, specialized protocol gateways, and carefully engineered communication paths. AppGate ZTNA addresses this challenge by focusing security at the access layer, rather than attempting to re-architect industrial networks.
Lightweight enforcement points can be deployed within or adjacent to OT environments, allowing organizations to create identity-defined access boundaries around critical systems. For legacy or unmanaged devices that cannot run endpoint agents, the AppGate Connector provides a secure bridge that enables policy-based access without exposing those assets to the broader network. Through this model, organizations can secure connectivity to PLCs, RTUs, industrial controllers, and other field devices while preserving the operational integrity of the plant network.
The result is a more resilient security posture that reduces the risk of unauthorized access, limits lateral movement, and protects critical infrastructure systems without introducing new operational dependencies.
Modernizing OT Access for the Next Generation of Industrial Operations
Industrial environments are undergoing rapid digital transformation. Remote monitoring, distributed engineering teams, and increasingly interconnected systems are changing how plants and critical infrastructure operate, even as the security risks associated with this connectivity continue to grow.
Traditional network-centric security models were never designed to support this level of connectivity in environments that depend on reliability and safety. Organizations need an approach that protects industrial systems without introducing operational fragility. By enforcing identity-based access control, cloaking infrastructure, and enabling direct, high-performance connectivity, AppGate ZTNA provides a practical path for extending Zero Trust into OT environments.
As remote access becomes an integral part of industrial operations, securing that access will be one of the most important steps organizations can take to protect the infrastructure that keeps the physical world running.
Ready to modernize OT access without disrupting operations? See how AppGate ZTNA secures industrial environments with identity-based controls and direct-routed connectivity.