Remote work, cloud adoption and the proliferation of mobile devices push traditional network perimeters to the edge and present new cybersecurity challenges for organizations worldwide. To better safeguard their clients’ networks, managed service providers (MSPs) are leveraging advanced Zero Trust Network Access (ZTNA) to redefine how their clients’ users securely connect to critical resources.
Why MSPs are replacing risky VPNs with ZTNA
The transformative operational and security benefits of ZTNA allows MSPs to offer robust, scalable secure access to handle the complexities of an interconnected digital world. In particular, ZTNA significantly outperforms risky “connect first, authenticate second” VPNs that breed risks like credential stuffing and open ports that threat actors can easily exploit to move laterally through a network.
Moreover, ZTNA introduces an unprecedented level of dynamic access control built on the Zero Trust security principle of least privilege ... granting access only to the resources authorized users require to do their jobs. ZTNA architecture also uses single packet authorization (SPA) to make resources invisible to unauthorized users, stop lateral movement and greatly reduce attack surfaces.
And it’s important to talk about scalability ... or the lack thereof. Reconfiguring VPNs to accommodate workforce or infrastructure shifts are a labor-intensive administrative burden for IT teams. But the dynamic access policies and agile architecture of ZTNA ensures MSPs can rapidly onboard new users, secure access to new applications or resources, or adjust access controls. This streamlined scalability not only saves valuable admin time for MSPs but also enables their clients to adapt quickly to changing business needs without compromising security.
Another key ZTNA benefit lies in an enhanced visibility and control over network traffic. Traditional VPNs often provide limited insight into user activities and network usage, making it challenging to identify potential security incidents or efficiently allocate resources. ZTNA delivers visibility with comprehensive audit logs and real-time data on user access which supports proactive anomaly detection, rapid threat response and the ability to fine-tune access policies. This means MSPs and their clients have a holistic understanding of network activity and can collaboratively optimize network performance and security.
Still thinking about switching from VPN to ZTNA? Here is a quick video case study with Jim Brittain of Ft. Worth-based Blue Jean Networks/Integris in which he discusses how Appgate SDP ZTNA solved the operational, security and connectivity issues of their old VPN. He also talks benefits like improved secure access control and remote monitoring and management services; reduced help desk trouble tickets for clients; and the ability to meet the conditional access requirements of cyber insurance companies.
Direct-routed vs. cloud-routed ZTNA
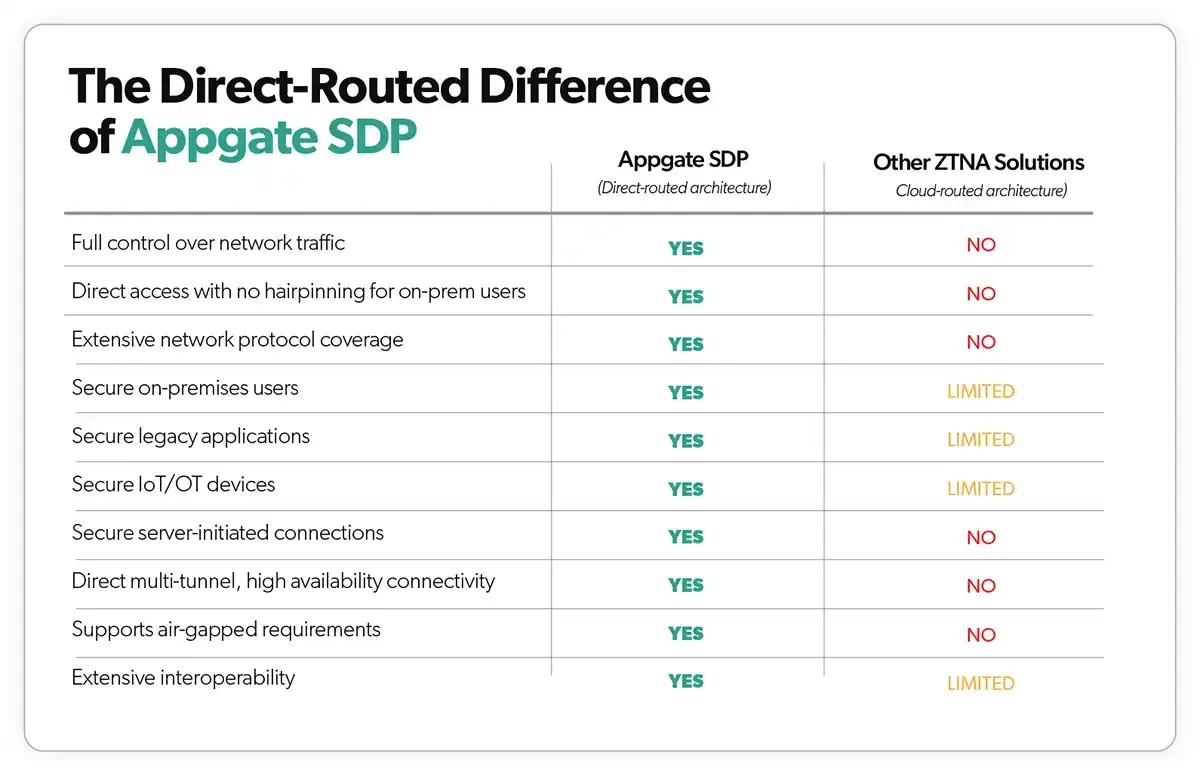
Now that we’ve illuminated the proven security and operational advantages of ZTNA over VPNs, it’s essential to know that not all ZTNA solutions are the same. MSPs shopping for a ZTNA solution should ask vendors this simple question: Is your ZTNA solution direct-routed or cloud-routed? Here’s why.
The majority of ZTNA solutions take a cloud-routed approach, utilizing a proxy-based architecture commonly referred to as identity-aware proxy (IAP), which directs all traffic through a vendor cloud. While these cloud-routed ZTNA solutions are effective at safeguarding remote connections to web applications, they were not specifically designed for intricate hybrid infrastructures and may not be suitable for all use cases. Specific cloud-routed ZTNA disadvantages include:
- Network traffic forced through vendor cloud
- Network protocol and on-prem resource constraints
- Throughput, scale, latency, and hair-pinning limitations
- Implicit trust of vendor multi-tenant cloud
- Hidden or variable costs
Conversely, direct-routed ZTNA advantages for MSPs and their clients include:
- Full control over network traffic
- Universal access control for all users, devices, and workloads
- Low-latency, high availability direct access
- Flexible deployment options for true Zero Trust architecture
- Predictable pricing
Our industry-leading Zero Trust access solution AppGate ZTNA is one of the only direct-routed ZTNA solutions on the market today. The unique direct-routed architecture ensures the flexibility, control, and extensibility required by MSPs and their clients to secure their whole environment, harden defenses, transform their network, and drive measurable ROI and value for the business
Ultimately, the right Zero Trust Network Access solution is a game-changing approach to network security that delivers a wealth of advantages for MSPs and their clients. By embracing ZTNA, MSPs can elevate their service offerings, enhance client satisfaction and solidify their position as security leaders in the competitive IT services landscape. You can learn more about Appgate’s global MSP program here.
Additional MSP ZTNA resources
What's the Difference Between Cloud-Routed and Direct-Routed ZTNA?
5-Step Guide to Simplify VPN to ZTNA Migration
How ZTNA Drives Successful Business Outcomes for MSPs and MSSPs