In today’s increasingly interconnected work, secure remote access is essential for organizations to stay competitive while providing greater visibility and control over critical systems and data.
How does secure remote access work?
Secure remote access allows users to access their computers and networks from anytime and anywhere globally, provided they have an internet connection. Typically, secure remote access solutions use encryption to secure data transmissions between users and their devices to corporate resources. Additionally, secure remote access solutions often use secure authentication methods, such as two-factor or multi-factor authentication, which require users to provide multiple pieces of identifying information before gaining access to corporate networks. Overall, secure remote access is a powerful tool that allows individuals and businesses alike to connect via devices to distributed network resources conveniently and reliably, no matter where they are.
What are the benefits of secure remote access?
Secure remote access provides many benefits for organizations and individuals. A secure remote access solution allows users to connect to their work networks at anytime from anywhere, using any internet-connected device. Secure remote access also helps improve security by ensuring that only authorized users can access an organization's sensitive data and systems. Finally, secure remote access is a valuable tool for anyone who needs to connect to their work network from outside the office.
Why is secure remote access important?
The workforce has changed dramatically, with an increasing number of people now able to conduct their jobs entirely from remote locations. This trend, known as the "hybrid workforce," poses new security challenges for organizations that must find secure and reliable ways to connect remote employees with the rest of the organization. One important tool that organizations can use to address these challenges is secure remote access.
By providing secure and fast access to critical business applications and data, a secure remote access solution empowers remote workers to stay connected anytime from anywhere. With the hybrid workforce trend continuing to grow, secure remote access is critical for organizations seeking to thrive in today's digital economy.
What is the most effective secure remote access solution?
Zero Trust Network Access is built on the more secure “authenticate first, connect second” principle of least privilege and is quickly becoming the standard for network access across the hybrid workplace for enterprise environments and workforces. In fact, according to Gartner, “by 2024, at least 40% of all remote access usage will be served predominantly by Zero Trust Network Access, up from less than 5% at the end of 2020.
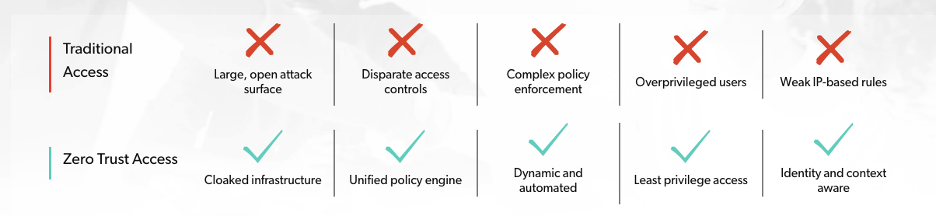
ZTNA is the most effective secure access method available. In contrast to the antiquated and insecure “default allow” mode of VPNs, NACs and firewalls, ZTNA takes a “default deny” approach to digital resources. ZTNA is built on three core pillars:
- Identity-centric: designed around the user identity, not the IP address, and requires user authentication before granting network access
- Zero Trust: applies the principle of least privilege to the network and users by using micro-segmentation to make unauthorized resources invisible
- Cloud-centric: engineered to operate natively in the cloud and deliver scalable security
And Zero Trust maturity is paying off, as stated in the Cost of a Data Breach Report 2021 by IBM Security and the Ponemon Institute. The average cost of a data breach was 35% lower ($1.76M) per breach for organizations in the mature stage of Zero Trust deployment compared to those without Zero Trust deployed.
Tips for evaluating a secure remote access solution
Zero Trust Network Access (ZTNA) is gaining popularity as a solution that applies Zero Trust principles to your network security. ZTNA inquiries from Gartner’s end-user clients increased more than 50% in 2021 compared to 2020, according to its report, How to Select the Right ZTNA Offering. What’s more, 62% of organizations that use ZTNA for specific purposes are actively expanding their usage or planning to expand their usage to replace virtual private networks (VPNs), according to ESG’s 2021 SASE Trends report.
Here are a few key factors to consider when evaluating a secure remote access solution built on the principles of Zero Trust:
- Complete protection that goes beyond secure remote access: Remote and in-office users; BYOD, corporate issued and IoT devices; cloud-native, legacy on-premises and traditional cloud workloads
- Single packet authorization (SPA): Cloaking ports so they aren’t visible to any user or device on the network reduces the attack surface and protects valuable resources
- Concurrent access: enables users to access resources in multiple environments without switching access solutions.
- Micro-perimeters: Role, time, date, location and device posture offer identity-centric factors that can inform least privilege access entitlements
- Robust APIs: Integration with existing systems can promote automation, enforce risk-based access and and break down silos
- Posture checking: Device risk context can help inform what level of access should be permitted
By considering these ZTNA factors, you can be sure to choose a modern solution that meets your secure remote access needs for now and the future. And you will be deploying a secure access solution that can easily adapt to securing access for all use cases, not just secure remote access.
Appgate SDP: A leading secure remote access solution
Appgate SDP delivers industry-leading Zero Trust Network Access to anything from anywhere by anyone. It requires users to be authenticated across a range of identity-centric and context-based parameters, such as role, time, date, location and device posture, before allowing access to enterprise resources … which prevents unsanctioned lateral movement.
Working with your existing security ecosystem to enforce Zero Trust principles, Appgate SDP features a single policy decision point that controls access across your organization’s entire IT ecosystem. In addition, exceptional API integrations mean less rip and replace and more augment and optimize to strengthen and simplify access controls by putting existing systems and data to work.
Learn how Appgate SDP stands out among other ZTNA solutions by attending our monthly ZTNA Table Talks live learning series. You can register here.
Additional secure remote access solution resources
Case study: The Third Floor Secures Remote Workforce
Podcast: Getting Real About Zero Trust
VPN Alternatives: It’s Time for More Secure Remote Access