Updated January 2024
VPN limitations became rapidly apparent during the pandemic as organizations rushed to secure fully remote workforces. Admin burdens, increased trouble tickets due to user sign-on issues, system crashes and significant security gaps proved that VPNs couldn’t secure an influx of remote users then, certainly can’t cover it now and aren’t the answer for the future.
This realization has sparked organizations to investigate Zero Trust Network Access (ZTNA) solutions that are proven to provide better remote access security. In fact, according to the Gartner report, How to Select the Right ZTNA Offering, “ZTNA inquiries from our end-user clients increased more than 50% year over year, driven by significant interest from multiple verticals, including government organizations. VPN replacement for extended-workforce remote access is the top use case.”
Let’s look at a few factors you should keep in mind when considering ZTNA vs. VPN.
ZTNA vs. VPN: Which is more secure?
A Consumer Reports evaluation of VPNs revealed that vendors’ sweeping claims fell short and confirmed what most of us already knew: “The industry’s privacy and security practices often don’t live up to its marketing.” And how many CVEs and zero-day attack warnings like those against Ivanti's Connect Secure VPN and Fortinet Fortigate VPNs have to happen and how much patching must be done before organization's realize there's not contest when it comes to comparing ZTNA vs. VPN ... Zero Trust Network Access is far more secure.
The biggest drawback of VPNs is that they all have open ports that are constantly listening and easily scannable by hackers. And they are hardware bound, so they can’t scale at the rapid pace of today’s cloud-first organizations.
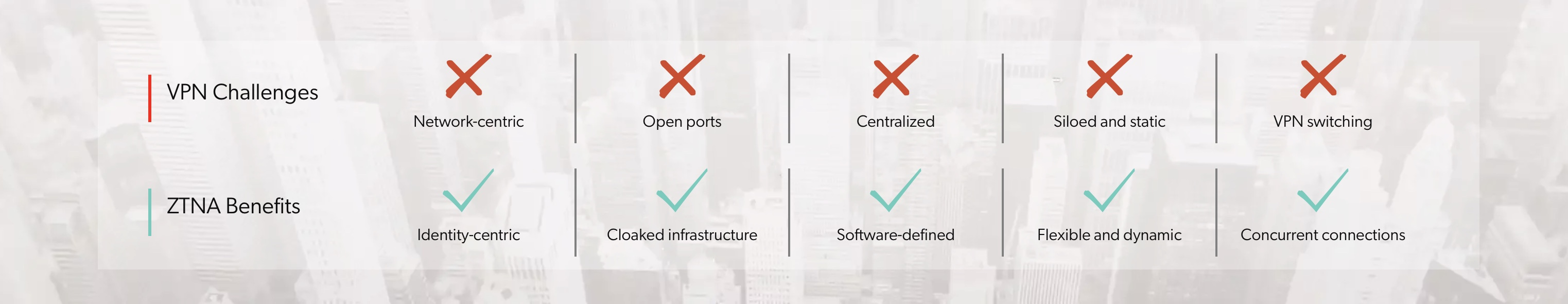
Agile Zero Trust Network Access is the secure remote access solution for now and the future because it’s identity-centric, software-defined, allows concurrent connections and cloaks infrastructure. Due to versatility and superior benefits compared to VPNs, ZTNA solutions are often an organization’s first step in a Zero Trust security journey.
At-a-glance: ZTNA vs. VPN
ZTNA vs. VPN: It’s not just about remote access
Adoption of ZTNA has increased, and not just as an alternative to VPNs. As organizations continue digital transformation projects, they’re sending more data, applications and workloads to the cloud. And cloud migration is another area in which ZTNA excels because it automatically scales with cloud workloads and eliminates the need for manual intervention as dynamic entitlements stretch across multi-cloud environments.
Access management is another key difference when evaluating ZTNA vs. VPN. Legacy VPNs don't follow the Zero Trust security principle of least privilege, instead giving users wide-open access ripe for lateral movement. This is a particularly important pain point in cloud entitlements, according to a study by CloudKnox, which reports 90% of identities were using less than 5% of permissions granted in 2021. ZTNA, on the other hand, offers unified Zero Trust policies, stronger access control and a reduced attack surface.
The least privilege principle of Zero Trust Network Access also extends to third parties like vendors, contractors and business partners. Third parties are a growing vector for breaches. More than half of respondents to the 2021 Ponemon Cost of a Data Breach report experienced a data breach due to a third party.
Another growing trend in cybersecurity is to inject security into DevOps teams, making DevSecOps the new path forward. ZTNA not only unleashes DevOps by offering concurrent access to hybrid cloud and cloud native environments, it also enables DevSecOps by delivering security as code and automating fine-grain access permissions in highly elusive cloud architectures. The same Zero Trust policies are applied to resource-to-resource connections found with microservices.
ZTNA vs. VPN Case Studies
Here are a few Appgate SDP customer success stories that support the fact that it’s really no contest in the ZTNA vs. VPN comparison game:
- DXC Technology, a Fortune 500 global IT services leader, initiated its Zero Trust journey to solve two issues: Reducing its network attack surface directly connecting to application environments and future-proofing its network infrastructure by downsizing multiprotocol label switching (MPLS) and VPNs.
- Jellyvision, a software company that’s reinventing how employees choose and use benefits, had a hardware VPN solution that was difficult to manage, vulnerable, restrictive and at the end of its life. With ZTNA, Jellyvision can enforce least privilege access, simple-to-configure entitlements and hide its infrastructure using single packet authorization (SPA).
- Datadog, a monitoring platform for cloud applications, went from two AWS accounts to 18, spread across more than 600 users in more than 100 locations. VPNs couldn’t enforce device validation and granted overly broad access, so the company adopted a Zero Trust model. Now users only have access to the specific resources that they need thanks to the precise, fine-grained access control of a ZTNA solution.
- The Third Floor, a top visualization studio in Los Angeles, kept production flowing as it transitioned 250 employees to a work-from-home model. ZTNA vs. VPN was never a debate for this forward-thinking studio. In four days, the company rolled out a ZTNA solution that provides secure access to the resources users need and protects intellectual property being created at the studio.
Appgate SDP, a clear ZTNA vs. VPN winner
Nemertes, a global research firm, released a study highlighting the operational benefits of Appgate SDP, an industry-leading ZTNA solution. Appgate SDP simplifies and strengthens access controls for all users, devices and workloads using its patented multi-tunneling technology to allow simultaneous and direct connections between users and resources regardless of location. Want to learn more? Get the eBook: 5 Steps for Successful VPN to ZTNA Migration.
Additional ZTNA vs. VPN resources
Blog post: VPN vs. ZTNA vs. SDP vs. NAC: What’s the Difference?
Data sheet: Secure Access for DevOps with SDP
Webinar: The Four Stages of Zero Trust Maturity