Despite changes in policy issuance and increases in premiums, enterprises still rely on cyber insurance to reduce the financial impact of ransomware and other malware. These insurance policies can cover first-party losses such as theft and data destruction, or third-party losses like liability stemming from failing to safeguard data.
In 2021, we saw several high-profile examples of malicious code, specifically ransomware, crippling sites and infrastructure in both the private and public sectors. As a result, insurers are taking a more cautious approach when issuing cybersecurity policies, and premiums have doubled in some regions.
Insurance companies no longer treat the issuance of cyber insurance policies as routine. What was once a process that consisted of a few questions can now be a long, involved due diligence exercise and sometimes risky applicants are denied coverage. And since legacy systems are almost always mission critical, they represent ripe targets.
The challenges of securing legacy systems
Many enterprises are lowering risks and cost by moving operations to the cloud, yet two facts keep emerging:
- Cloud security isn’t included out of the box
- Not everything is, nor CAN be, in the cloud
In fact, massive transactional processes are still run on legacy hardware systems heavily relied on by industries like banking, insurance, healthcare and retail. Some of the most familiar models are the AS/400 and iSeries by IBM. These systems also run legacy applications, sometimes in programming languages no longer taught in colleges. These systems keep our ATMs operating, track our flights and ensure that the cost of a one-quarter inch bolt at a big box hardware store is up-to-date.
But people don’t access these systems using dumb terminals any more. They are accessed with the same devices used for modern apps, on the same networks, and are vulnerable to the same exploits and threats. And then there are industrial control systems (ICS), the precursor to IoT, that routinely turn valves in a plant, check a patient’s insulin levels and operate plant security gates from embedded operating systems often installed on chips.
Securing these legacy systems from modern threats have remarkably similar problems. How do you secure a mini against APTs? How do you upgrade a device operating on a hardware version of Windows 3.0? Traditionally, these systems were physically segmented from general purpose networks. But this solution creates inefficiency and bottlenecks, requiring administrators to manage multiple network and access systems. Invariably, efficiency requirements mean these networks get linked or bridged and suddenly an unsecured HVAC system is connected to the point-of-sale system at a major retailer.
How can you secure access for scattered resources and reduce your risk?
The answer is to update secure access solutions so you can adequately safeguard hybrid network infrastructure. First, remove outdated, perimeter-based defenses like VPNs. Second, go beyond antiquated username and password authentication, and implement modern, multi-factor authentication (MFA) supported by robust identity and access management (IAM). Third, and most importantly, apply that MFA process to all resources … cloud, on-premises and legacy systems included.
How can you accomplish all three? With Zero Trust Network Access (ZTNA) that integrates IAM authentication and adds continuous posture monitoring, you can address security at multiple levels:
- Who or what is seeking access? Verify identity.
- Where are they? Gather context.
- What is their operating environment? Assess risk.
- What resources should they have access to? Apply policy.
- Has anything changed? Dynamically adjust entitlements.
MFA, applied to not just modern resources, but your entire infrastructure, represents the best protection against current and future cyberthreats. And increasing your security posture against cyberthreats is a tangible way to reduce risk, which cyber insurance policies should reflect.
Use Case: Financial systems legacy apps
Let’s take a look at the proven risk reduction of Appgate SDP, an industry-leading ZTNA solution. One of our customers is a global 500 financial organization that relies on legacy applications for day-to-day business operations. However, these legacy applications could not be readily integrated with MFA solutions running on IAM platforms without a cost prohibitive refactoring of the entire system. The organization was challenged with ensuring secure access to the high-value legacy applications that complied with regulatory requirements, including modern methods of user authentication (such as Security Assertion Markup Language or SAML).
Serving as a pass-through to apply MFA, Appgate SDP natively integrated with the organization’s IAM solution to secure user access between the organization’s legacy and modern applications and address compliance and regulatory requirements, which also supports cyber insurance requirements.
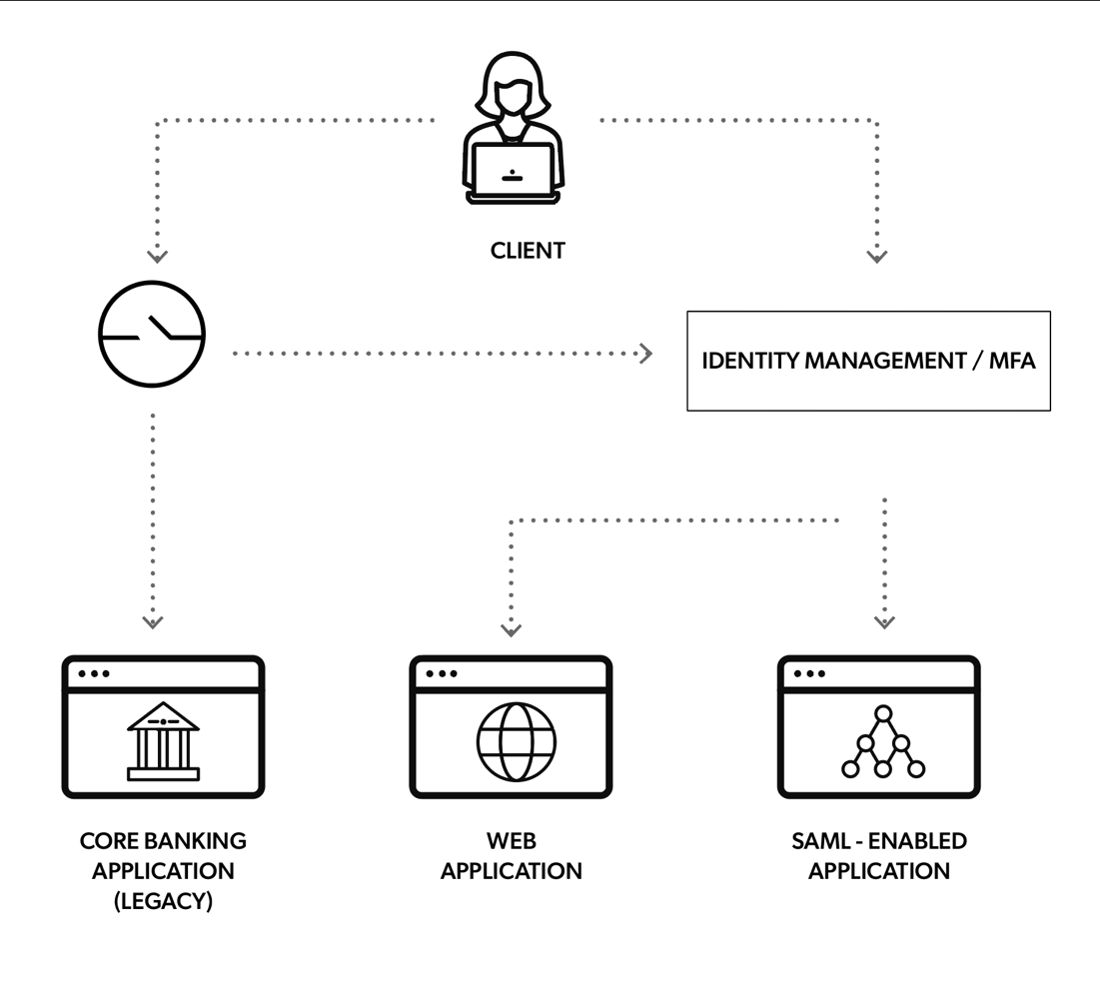
Here we illustrate how an employee of the financial services organization accesses a legacy application that cannot utilize SAML or MFA.
- To access the application, the employee is authenticated and authorized to access specific network resources with Appgate SDP.
- Appgate SDP consumes the SAML authentication. The user is authenticated and granted access to the legacy application.
- The only pathway to access the legacy application is through Appgate SDP.
- It protects the system from network access through any other means, ports or connections.
Ultimately, insurance companies base their policies and premiums on risk score. Drivers who get multiple speeding tickets pay higher premiums than those who never get pulled over – and sometimes, multiple offenders are denied coverage entirely. Cyber insurance is no different, and the best bang for the buck in reducing the threats imposed by cybercriminals is a robust Zero Trust implementation. So, you can reap two benefits with Appgate SDP: you can secure both your legacy systems and modern apps, and ultimately present a justification for lowering your cyber insurance premiums.
Additional resources:
Case Study: Financial Services Institution Protects Legacy Assets with Appgate SDP
Podcast: Is Zero Trust Security a Buzzword or a Breakthrough?
eBook: Zero Trust Maturity Model Roadmap