Updated 1/23/2023
Perimeters as we once knew them are gone. Infrastructure is no longer centralized on premises and users, whether employees or vendors, are connecting to enterprise resources from home offices, airports and coffee shops. Security tools like legacy VPNs, firewalls and network access controls (NACs) are obsolete. This is where software-defined perimeter solutions step in.
What is software-defined perimeter (SDP)?
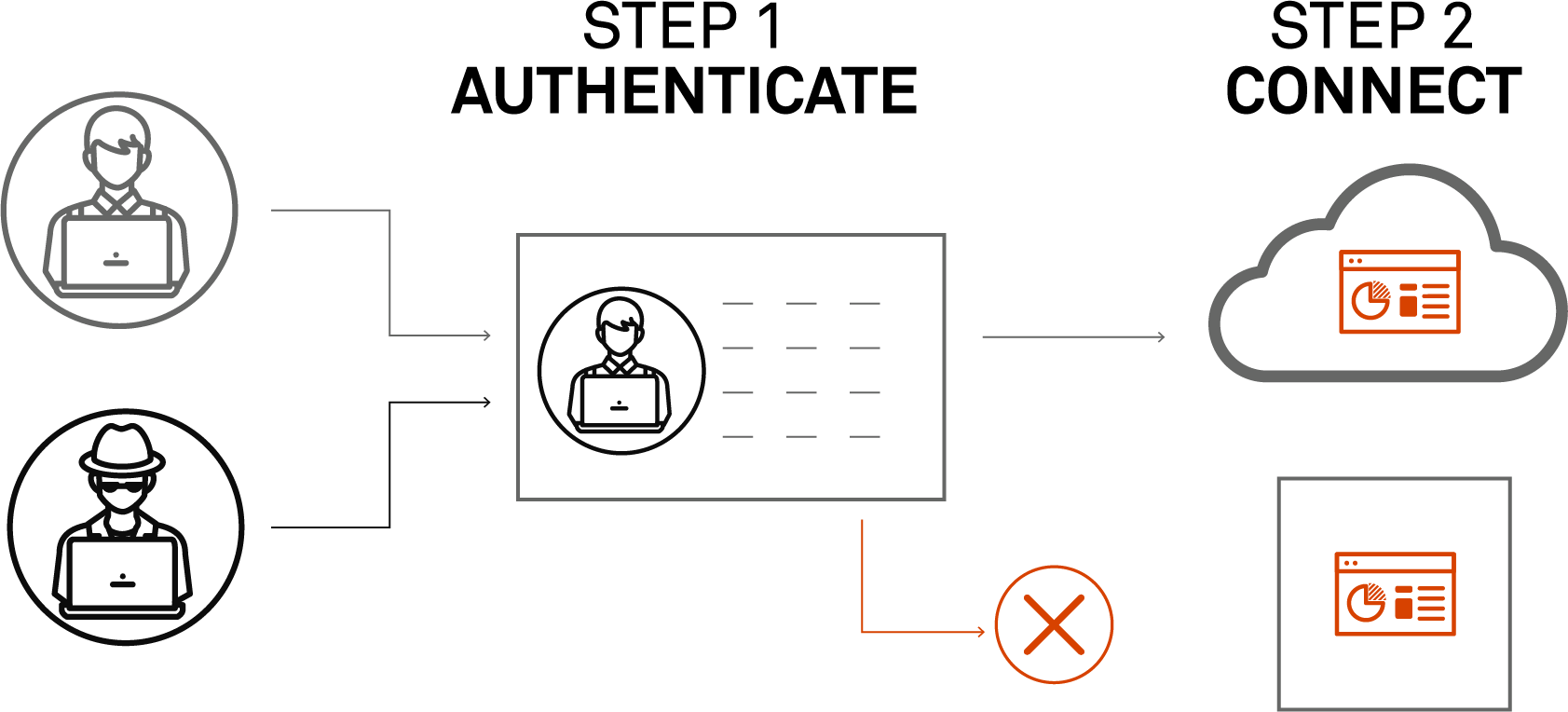
Based on work by the U.S. Department of Defense (DoD), software-defined perimeter is a security framework designed to micro-segment network access. SDP dynamically creates one-to-one connections between users and the resources they access. Software-defined perimeter and ZTNA refer to a proven, more secure “authenticate first, connect second” network cybersecurity strategy.
Overview: How does SDP work?
SDPs protect servers by making it impossible to connect without authorization. They do this by 1) verifying the user's identity; and 2) assessing the state of their device. Unlike traditional network security that connects various roles or groups to a network segment and then relies on application-level permissions for authorization, software-defined perimeter solutions create individualized perimeters for each user, allowing for more fine-grained access control.
Unlike traditional network security that connects various roles or groups to a network segment and then relies on application-level permissions for authorization, software-defined perimeter solutions create individualized perimeters for each user, allowing for more fine-grained access control.
The benefits of a software-defined perimeter
Put simply, software-defined perimeter is a trusted, comprehensive, robust and adaptive solution that modernizes enterprise network security to:
- Strengthen and simplify access controls
- Reduce attack surfaces
- Remove policy management complexity for admins
- Improve end-user experience
- Unleash operations with integrations and automation
Why do you need software-defined perimeter network security?
Traditional network security solutions can’t keep up with the speed of digital transformation, distributed workforces, or increasingly sophisticated threat actors. All-or-nothing access controls, like VPNs, leave you vulnerable because users have overly privileged network access that increases your attack surface and overall risk.
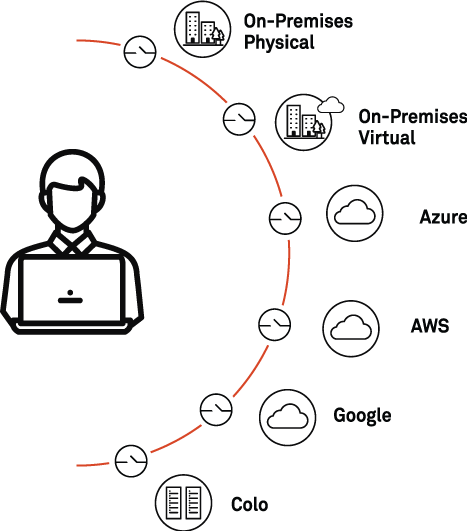
It’s time for an identity-centric, Zero Trust approach to defend against evolving cyberthreats. A software-defined perimeter reduces over-privileged access and third-party risk, safeguards DevOps without restrictions and secures access to critical workloads located on-premises, in the cloud, across hybrid IT ecosystems or even in those dusty—yet still utilized—mainframes.
What are the details of how a software-defined perimeter works?
When examining the question “what is a software-defined perimeter?”, it’s important to understand how these types of network security solutions work. They’re built on three core pillars:
- Identity-centric: Designed around the user identity, not the IP address, and requires user authentication before granting network access
- Zero Trust: Applies the principle of least privilege to the network and users by using micro-segmentation to make unauthorized resources invisible
- Cloud-centric: Engineered to operate natively in the cloud and deliver scalable security
Software-defined perimeter ensures all endpoints attempting to access enterprise infrastructure are authenticated and authorized before access is granted to any network resource. This applies the principle of least privilege and reduces your attack surface by hiding network resources from unauthorized or unauthenticated users.
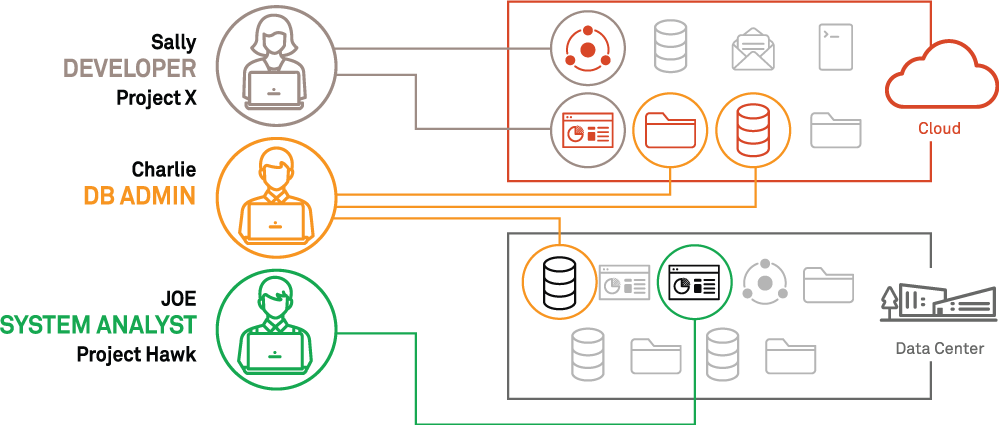
SDP supports the speed and agility demanded by digital transformation and unforeseen market pressures. You can spin up tens of thousands of cloud servers across the world, grant specific access for a defined user group or an individual to a particular data set then pull back those rights hours later. A software-defined perimeter solution interrogates the environment and pulls back metadata to identify new or changed resources and automatically creates entitlements for the proper users. SDP is as fast and as scalable as the cloud itself.
A rally cry for Zero Trust security principles and software-defined perimeter methodology
Implementing Zero Trust security built on software-defined perimeter is the new standard; even the government has prioritized it. A White House executive order requires federal government agencies to “develop a plan to implement Zero Trust architecture” as defined by National Institute of Standards and Technology (NIST).
According to the Cloud Security Alliance (CSA) software-defined perimeter working group, SDP is agnostic of the underlying IP-based infrastructure and focuses on securing all connections using that infrastructure, therefore it is the optimal methodology for achieving a Zero Trust network.
In addition, industry analysts tout software-defined perimeter and ZTNA due to the proven ability to harden your cybersecurity defenses, ease operational burdens and deliver a frictionless user experience.
As traditional access control solutions fail, organizations are quickly realizing that a ZTNA software-defined perimeter solution is the best alternative to protect sophisticated, complex and dispersed hybrid enterprise environments. In fact, according to Gartner, “By 2024, at least 40% of all remote access usage will be served predominantly by zero trust network access (ZTNA), up from less than 5% at the end of 2020. While most of these organizations will not completely retire all their client-facing VPN services, ZTNA will become the primary replacement technology.”
Not all software-defined perimeter vendors are created equal
Many software-defined perimeter vendors claim ZTNA advantages but can only handle remote access and won’t scale to meet hybrid enterprise requirements for uniform access from any location, including the main office. For instance, many software-defined perimeter vendors don’t enforce the principles of Zero Trust when users are in-office and struggle to secure anything beyond web-app protocols.
Why Appgate SDP should be your ZTNA vendor of choice
Appgate SDP is an industry-leading, enterprise-grade ZTNA solution that puts your people first with simple, fast, secure connections to anything from anywhere by anyone, anytime. Benefits include:
- Strengthened security: Reduces attack surfaces, verifies user identities, prevents lateral movement and secures east-west traffic.
- Reduced complexity: Customers see a 91% average reduction in user provisioning time (according to the Nemertes Real Economic Value study referenced below)
- Improved end-user experience: Improved performance and ease of use including maintaining concurrent connections to many applications
- Streamlined automation: Automates policies and infrastructure, orchestrates workflows and puts data to work.
Appgate SDP was named a Leader in the The Forrester New Wave™ Zero Trust Network Access, Q3 2021 receiving a differentiated rating, the highest possible, in six criteria including deployment flexibility, non-web and legacy app support, ecosystem integration, client support, connector capabilities and product vision. Additionally, in the Nemertes Real Economic Value study, Appgate SDP customers reported a 119% average increase in accelerated digital transformation initiatives, a 9.5 out of 10 rating for “most strategic to Zero Trust” and an average 66% reduction in help desk tickets.
Are you evaluating ZTNA vendors? The best way to understand how Appgate SDP works and learn more about its advantages over other software-defined perimeter solutions is to schedule a demo with one of our experts; attend a live demo; take a 20-minute guided experience; or watch bite-sized demos.
Additional Zero Trust Network Access and SDP resources:
Blog: Universal ZTNA: Zero Trust Network Access Comes of Age
eBook: 5-step Guide for VPN to ZTNA Migration
Solution brief: Zero Trust Access for Corporate Networks
eBook: Zero Trust for the Cloud
Podcast: The Four Stages of Zero Trust Maturity