Enterprise security and IT teams have faced storm clouds of change when it comes to delivering secure access for people to the resources needed to do their jobs. First, it was a seemingly overnight shift to work from home and battling antiquated VPNs that couldn’t handle the surge. Then cybercriminals upped the ante with relentless ransomware and phishing attacks to find escalating security gaps and target the No. 1 attack vector, people. Now it’s a question of how to adequately secure access for hybrid workforces connecting from anywhere to hybrid workloads housed everywhere.
However, the silver lining over the past few years is that many organizations weathering the cybersecurity storm have turned to the proven security advantages and operational and business benefits of Zero Trust Network Access. In fact, enterprises are rapidly deploying universal ZTNA across the full corporate network as this revolutionary secure access solution comes of age.
What is universal ZTNA?
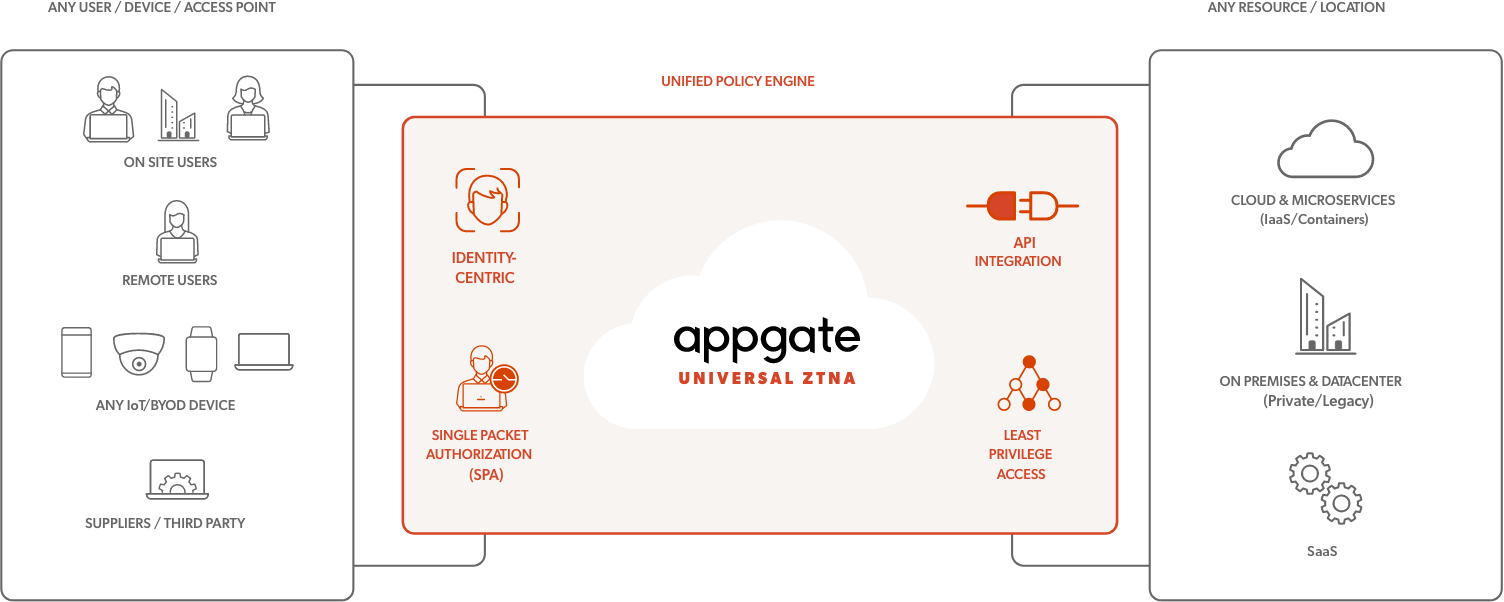
ZTNA doesn’t just solve for remote secure access use cases ... it has matured to support on-campus and on-premises users and devices including IoT. So, what is universal ZTNA, or as we like to call it, Zero Trust Network Access anywhere?
Universal ZTNA, a term coined by Gartner, is the most effective secure access method available. In contrast to the “default allow” mode of VPNs, network access control (NAC) solutions and firewalls, universal ZTNA is based on the principles of Zero Trust, which takes a “default deny” approach to digital resources. However, not all ZTNA solutions are created equal. The most effective ZTNA solutions address more than just remote access, which many security vendors viewed as the only factor to consider early on and now they are desperately trying to pivot their architecture and features to also solve for universal ZTNA. Many of these same vendors also built architectures that only supported cloud access, making it even more difficult to solve for on-campus users and devices.
On the other hand, comprehensive universal ZTNA solutions safeguard access across your entire ecosystem of users, use cases, workloads and full corporate network, not just the parts that are in the cloud. And they will readily adapt to your “now and next” digital transformation and cloud initiatives and unforeseen external forces of change. As users and employees come back into the office post pandemic, they expect the same level of simplicity of use they got working remotely, and security teams want to enforce the same level of access policy in the office.
Why universal ZTNA and why now?
On campus and WFH workforces and a mixture of legacy, on-premises and multi-cloud workloads plus IoT devices mean that enterprises must overcome many security hurdles:
- Traditional cybersecurity systems were built for high-trust, perimeter-centric environments, making them ill-equipped to protect an expansive, ever-changing attack surface created by work-from-anywhere policies and dispersed IT environments
- Legacy workloads on midrange and mainframe equipment are difficult to add modern security and expensive to refactor but must still be accessible
- Unmanaged or compromised devices that act as unwitting attack vectors and lack strict controls (e.g., BYOD, IoT and OT)
- Notoriously complex cloud environments lead many IT teams to default to permissive policies
Let’s also not forget about overburdened security and IT teams need modern secure access solutions that streamline administration, reduce complexity and enable business agility. And remote, in-office and third-party users need to be able to simply connect to wildly diverse on-premises, legacy and cloud environments without delays and disruptions. Providing all users with a unified, seamless experience, regardless of where they are working or where the resource is located, improves productivity and reduces the volume of trouble tickets.
To be clear, universal ZTNA is not new. The label is new and helps the industry move past pigeonholing ZTNA as a remote access-only solution. As organizations mature their Zero Trust programs—likely tackling remote users as the most logical and vulnerable starting place—universal ZTNA, or ZTNA anywhere, is a defining term to reinforce the criticality of extending Zero Trust principles across campus and branch networks.
Top reasons to consider universal ZTNA
The universal ZTNA market is flourishing because organizations are tired of cobbling together traditional security solutions that are insecure, wrack up help desk trouble tickets and aren’t built on the principles of Zero Trust security and least privilege access. What are the top reasons you should consider applying Zero Trust Network Access anywhere and everywhere across your full hybrid infrastructure?
- It’s identity-centric: ZTNA anywhere ensures we know as much about a user and/or the device as we can before allowing them to make a connection to the network, such as:
• What is the user’s context?
• What device are they using?
• What is the device’s security posture?
• Where is the user located?
What to look for in a universal ZTNA solution?
While ZTNA anywhere is the goal, not all Zero Trust Network Access solutions were architected to handle the sophistication required to cover remote and campus networking simultaneously. In fact, in a recent report, Gartner identified several issues that might apply to a limited ZTNA solution, such as:
- Lack of protocol support
- Securing headless devices, such as IoT
- Lack of support for bi-directional security rules
Specifically, streamlined advantages of advanced universal ZTNA solutions should include:
- Concurrent secure access for all users, devices and workloads wherever they reside
- Cloaking resources until a user is authenticated
- Maintaining policies in synch with dynamic infrastructure
- Micro-segmentation to deliver 1:1 secure access for users, devices, networks and resources
- Customization through a rich feature set, including APIs, which aligns with central IT requirements and processes
- A single framework and consistent configuration to unify access and minimize administrative tasks
- The ability to secure all network access, including on-premises, IoT/OT, WAN and campus networks
Questions to ask during the universal ZTNA vendor selection process
There are a lot of claims out there, so how can you be sure that a ZTNA vendor is up to the task of Zero Trust Network Access anywhere. Here are some questions to add to your universal ZTNA RFP process:
- Can your ZTNA solution work for in-office users?
- Can your ZTNA offering protect legacy infrastructure and modern cloud-native microservices?
- Does your ZTNA solution require connections pass through the vendors cloud, or do you have a choice of deployment models for your unique situation?
- How scalable is your ZTNA solution? Will it be able to meet my needs in six months or a year?
- What API integrations are built in to ensure seamless integration with our current tech and security stack?
- We’ve got an identity access management (IAM) platform. Can your universal ZTNA solution work with that?
- Does your ZTNA solution constantly monitor and dynamically adjust connections when risks change?
- What is the process for verifying a user’s identity and granted permissions?
- How does your ZTNA offering manage and enforce unified policies for users or IoT devices connecting to on-premises and cloud resources?
- How do policy changes work? Does your universal ZTNA solution reduce complexity by eliminating redundant or old policies?
- How does your product protect against lateral movement?
- Does your solution provide a unified and seamless experience for a user that is remote today and in the office tomorrow?
- What does network monitoring look? What kind of visibility will it offer my administrators?
Why Appgate SDP leads the universal ZTNA market
Appgate SDP stands out from other universal ZTNA vendors because it was architected to support on-premises users and resources, making it the most feature-rich and comprehensive solution available on the market today. Built to strengthen and simplify network security and simply secure user-to-resource and resource-to-resource connections, Appgate SDP was positioned highest for current offering in the Forrester ZTNA New Wave. Notably, in the Nemertes Real Economic Value study, Appgate SDP customers reported a 119% average increase in accelerated digital transformation initiatives, a 9.5 out of 10 rating for “most strategic to Zero Trust” and an average 66% reduction in help desk tickets.
Additionally, our cloud-native, cloud-delivered Zero Trust platform and built-in risk engine is designed to help enterprises easily deploy and maintain a cohesive security ecosystem, maximize existing investments and accelerate their Zero Trust security maturity. The multi-tenant platform speeds Appgate SDP deployment with a unique as-a-service approach that retains customer control of network traffic and reduces infrastructure management overhead. And the Zero Trust platform’s featured risk engine service enhances access policies with rich security context via click-to-configure connections to third-party IT, security and business solutions.
Learn more about the unique properties of Appgate SDP by watching this Appgate SDP introductory demo on-demand at your leisure.
Additional universal ZTNA resources
Podcast: Bringing Zero Trust Access to the Corporate LAN
Blog post: Hybrid Cloud Security and the Role of Zero Trust Network Access
Video on-demand: Kill the NAC – Zero Trust Access for the Corporate Network
eBook: Securing the Hybrid Enterprise